Darknet Markets 2026:
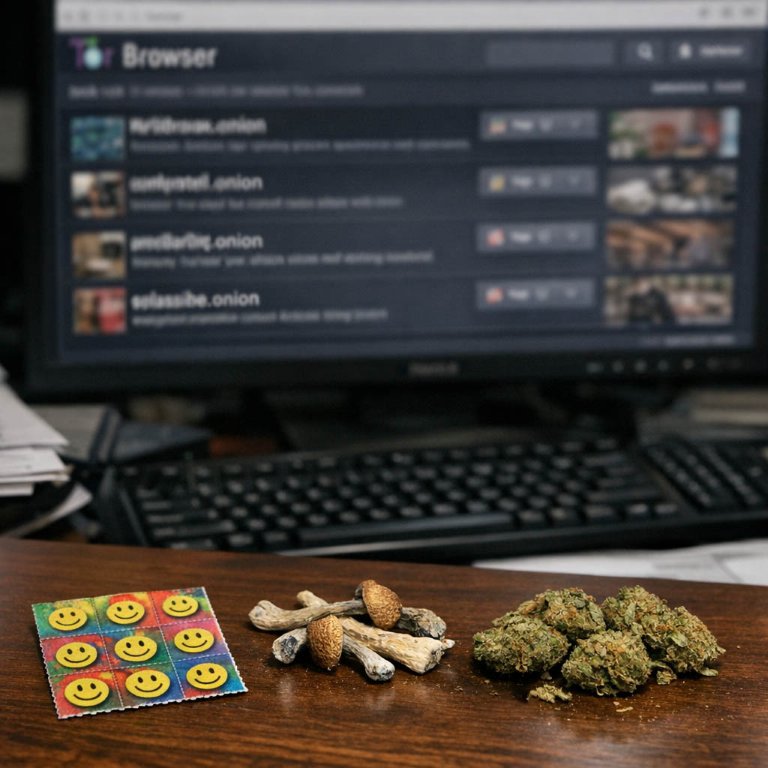
The dark web is part of the deep web but is built on darknets: overlay networks that sit on the internet but which can't be accessed without special tools or software like Tor. Tor is an anonymizing software tool that stands for The Onion Router — you can use the Tor network via Tor Browser.
| Darknet Market | Established | Total Listings | Link |
|---|---|---|---|
| Nexus Market | 2024 | 600+ | Onion Link |
| Abacus Market | 2022 | 100+ | Onion Link |
| Ares | 2026 | 100+ | Onion Link |
| Cocorico | 2023 | 110+ | Onion Link |
| BlackSprut | 2023 | 300+ | Onion Link |
| Mega | 2016 | 400+ | Onion Link |
Updated 2026-05-05
How Escrow and Multisig Wallets Make Darknet Trade Safer
Successful darknet commerce relies on systems that replace traditional legal guarantees with cryptographic ones. The escrow service is fundamental. When a buyer places an order, their payment is held by a neutral third party, the market's escrow system, until the goods are received and confirmed. This protects the buyer from vendors who might not ship products and protects honest vendors from fraudulent chargeback claims common in other online spaces.
Multisignature wallets enhance this model by distributing control of the funds. A typical 2-of-3 multisignature setup involves three keys:
- one held by the buyer,
- one by the vendor,
- and one by the market.
How Reviews and PGP Keys Build Trust on the Darknet
The reliability of a darknet vendor is the primary concern for any transaction. Two systems work in tandem to establish this reliability: a transparent feedback mechanism and cryptographic identity verification. The vendor review system functions as a continuous audit. Previous buyers detail their experience with product quality, shipping speed, and stealth. A vendor with hundreds of positive reviews over months or years demonstrates a consistent operational history. Negative reviews are equally critical, highlighting issues like poor communication or substandard materials. This collective intelligence allows new buyers to make informed decisions, creating economic pressure on vendors to maintain high standards.
Reviews alone can be falsified. This is where PGP verification becomes essential. Every reputable vendor maintains a unique PGP public key on their profile. This key is used to encrypt sensitive information, such as a shipping address, ensuring only the intended vendor can read it. More importantly, it provides cryptographic proof of identity. Before finalizing a purchase, a buyer must verify that the vendor's PGP key displayed on the market matches the key the vendor has publicly advertised on their own channels or past sales. This step confirms you are dealing with the legitimate vendor and not an impostor who has hijacked a listing. The combination of social proof from reviews and mathematical proof from PGP creates a robust framework for trust. It allows commerce to proceed between anonymous parties by making reputation a valuable, verifiable asset.
How Darknet Markets Stay Online and Secure for Reliable Trade
A resilient darknet market operates on infrastructure designed to withstand failures and attacks. This begins with server architecture. Leading platforms use a distributed server model, often across multiple jurisdictions, making a single takedown point ineffective. If one node is compromised, the service automatically reroutes traffic to others, maintaining maximum uptime.
This is complemented by robust DDoS protection. Markets employ specialized services and custom software to absorb massive floods of traffic intended to knock them offline. For users, this translates to consistent access without frequent downtime notices.
Attack resistance also depends on operational security (OpSec) for administrators. Markets that succeed long-term separate financial, technical, and support roles. This limits the damage if one individual is compromised. The codebase itself is often open-source or heavily audited by the community to prevent backdoors.
Finally, a key design element is the decentralization of escrow. Instead of holding all funds in one central wallet, advanced systems use a network of multisignature escrow agents. This removes a single, lucrative target for an exit scam and distributes trust, making the entire ecosystem more attack-resistant and stable for daily trade.
How Tor and Monero Keep Your Darknet Shopping Private
Integrated Tor routing is a foundational security layer for any darknet platform, ensuring all traffic between the user and the market is encrypted and anonymized by default. This design removes the technical burden from the user, preventing accidental exposure of their network identity or location. For financial privacy, coin mixers or tumblers are often provided as a service. These tools break the transaction trail on transparent blockchains like Bitcoin by pooling and redistributing funds, effectively obfuscating the link between the market deposit and the original source of the coins.
The combination is enhanced when using Monero (XMR). Its blockchain inherently provides privacy through ring signatures and stealth addresses, making the use of a separate mixer for the cryptocurrency itself largely redundant. A direct Monero transaction from a user's private wallet to the market's address contains no publicly visible information about the amount, sender, or receiver. This simplifies the process:
- Integrated Tor protects network-level data.
- Monero's protocol protects the financial transaction on the ledger.
This layered approach significantly reduces operational risks. It allows for discreet procurement of goods by separating the user's real-world identity from both their online activity and their financial transactions. Markets that facilitate this through built-in tools and Monero acceptance provide a more secure environment for commercial exchange.
Simple Layouts and Smart Search for Better Darknet Shopping
An effective darknet market prioritizes a user-centric design that reduces operational friction. A clean, intuitive interface is not merely aesthetic; it minimizes user error during critical steps like order placement or PGP decryption. Logical categorization of products, consistent navigation menus, and clear visual hierarchies allow users to conduct transactions efficiently. This design philosophy directly supports safety by ensuring that all users, regardless of technical expertise, can navigate the platform without confusion, thereby correctly utilizing the security tools provided.
The search functionality acts as the core tool for product discovery. Advanced filters are essential, allowing precise sorting by:
- Vendor reputation score and number of completed sales
- Product price, quantity, and destination country
- Shipping options and expected delivery timeframes
This operational efficiency is enhanced by financial privacy. The integration of Monero (XMR) complements the streamlined interface by offering a simple, private payment method. Unlike transparent blockchains, Monero transactions obfuscate sender, receiver, and amount by default. For the user, this means the payment step is as straightforward as using Bitcoin but without the need for external coin mixers. The market's wallet handles the technical complexities, presenting the user with a single XMR address for deposit. This seamless integration of privacy into the payment workflow means security does not come at the cost of usability, supporting a smooth and discreet commercial exchange.
How Monero's Privacy Makes Darknet Commerce Safer
Monero (XMR) functions as the preferred currency for private transactions on darknet markets due to its inherent cryptographic privacy features. Unlike transparent blockchains like Bitcoin, Monero obscures all transaction details by default. This is achieved through three core technologies: stealth addresses, ring signatures, and Ring Confidential Transactions (RingCT).
Every Monero transaction automatically generates a one-time stealth address for the recipient on the blockchain, making it impossible to link payments to a user's public view key. Ring signatures mix a user's transaction with several others, obfuscating the true source of funds. RingCT hides the actual transaction amount. These features collectively ensure that:
- Sender and receiver addresses are concealed.
- Transaction amounts are private.
- The history of any given coin is untraceable.
For darknet commerce, this provides a significant security advantage. It breaks the chain of evidence that external observers could follow on a public ledger. A buyer's financial activity cannot be linked to their market account or to the specific vendor they patronize. This design protects all parties from blockchain analysis, a common method used to deanonymize transactions on other networks. The privacy is protocol-level and mandatory, requiring no extra steps from the user, which reduces operational security errors. Markets that integrate Monero natively offer a more secure environment by leveraging these cryptographic guarantees, making financial tracking impractical and fostering greater trust in the transaction process.